12-30-2014
As technology advances and more companies turn to computer software to digitally process their data, a great deal of those companies overlook a very critical business process known as Configuration Management[1]. At a high level, Configuration Management (CM)[2] is the process of managing and tracking all changes within an entity, be it an individual server or an entire organization. It can quickly become a complex and labor intensive process, however implementing the basic fundamentals matter most. The official definition as stated by the National Institute of Standards and Technology (NIST)[3] is as follows:
Configuration Management (CM) comprises a collection of activities focused on establishing and maintaining the integrity of products and systems, through control of the processes for initializing, changing, and monitoring the configurations of those products and systems.
Over the course of the past ten years, we have observed companies, large and small overlook this process as a whole or mismanage the process by not segregating duties through several individuals, inherently introducing significant risk to the organization. As a result, lack of proper CM has resulted in non-functional software, data errors, system downtime, compromise of data and even financial fraud within an organization.
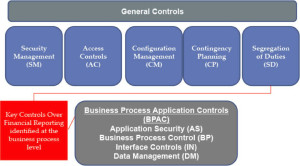
To minimize these costly risks it is important to incorporate a CM process to properly manage changes within your organization. Luckily, this process can be tailored to your organization depending on size and capabilities. NIST has a significantly detailed publication titled NIST SP 800-128, Guide for Security-Focused Configuration Management of Information Systems which covers CM in large, complex environments along with the controls to periodically check that the process is working as it should in a separate publication titled NIST SP 800-53, Revision 4, Security and Privacy Controls for Federal Information Systems and Organizations[4]. In addition, the Committee of Sponsoring Organizations of the Treadway Commission (COSO) offers a less detailed, financially focused framework[5] for managing a CM process.
However, if you do not have time to go through the processes mentioned above in great detail, or feel like your organization has not reached the level of where you would need to implement such a large effort to manage a small amount of changes to your IT environment, the following three steps could help start in developing your own CM process[6]:
- Identify any risks and gaps in the current process for implementing and managing changes. Several factors to consider are as follows:
- Does your organization currently have a CM process?
- Understand the basics of the CM flow (documented in NIST 800-128 and COSO)
- Identify and accept or mitigate your risks before beginning to develop your new CM process. Such examples are as follows:
- Does your organization currently have only one individual who is responsible for creating and implementing all changes within your IT environment? If so, this is a risk and will need to be mitigated. Examples we have seen in the past include separating duties and having a supervisor approve all changes before they are implemented into the production environment. In addition, changes included enforcement of separation, such as removing administrative access for programmers or implementers of changes.
- Do you track all changes? If so, are they consolidated and reviewed on a periodic basis?
- Do you keep backups of software or code before implementing new changes?
- Do you have separate test and development environments for your software in order to test changes before implementing them into production?
- Do you have a patch management process? Is your patch management process documented?
- Develop your new process:
- Develop a tailored draft CM process from the fundamentals mentioned in in NIST 800-128 and COSO, the process should cover the CM controls in COSO and/or NIST 800-53, rev 4.
- Discuss your new draft CM process with all appropriate divisions, management and stakeholders involved in your business. Additional tailoring might be required based on management’s guidance and recommendations.
- Test the process from start to finish
- After successful testing, implement your newfound CM process and make the entire organization aware of the changes.
- Continually monitor your process as you grow:
- Conduct patch management on your IT infrastructure.
- Conduct periodic vulnerability assessments on your IT infrastructure.
- Periodically review all changes for completeness and adherence to the CM process that you helped develop. This will help catch errors and also ensure that staff are following the new CM process.
- Revisit your CM process and periodically check for updated guidance from NIST or COSO. Make any changes or updates as necessary to improve the process.
The steps above are general and will help you get started. Each organization will have to tailor these steps based on internal policies and procedures. Each organization will also add or remove steps that do not present a risk at the time. In addition, implementing these steps will not guarantee that you will pass an IT audit. They only serve as guidance for starting the development of a CM process. For assistance in understanding the requirements of an IT Audit or for help getting optimal results, please contact us.
All organizations must implement some form of CM to manage changes to their systems and applications in order to reduce the risks mentioned above. Implementing an effective and efficient CM process will reduce[7] risks such as financial fraud, compromise of confidential data, non-functional software, data errors and costs associated with user downtime that come with implementing newer software and technology within your organization. As always, if you or someone you know needs assistance in understanding or implementing a new CM process, please do not hesitate to contact us at [email protected].
————————
[1] For the purposes of this article, we will use the term Configuration Management.
[2] We are referring to the IT Configuration Management process as opposed to the engineering Configuration or Change Management process.
[3] NIST SP 800-128, Guide for Security-Focused Configuration Management of Information Systems, August 2011.
[4] NIST SP 800-53, rev.4, Security and Privacy Controls for Federal Information Systems and Organizations, April 2013.
[5] COSO, The 2013 COSO Framework & SOX Compliance, One Approach To An Effective Transition, June 2013.
[6] Before making any changes and/or implementing any processes into your organization, always consult with your IT Security and IT Audit departments.
[7] Although implementing a CM process will reduce certain risks, it does not eliminate them. Many other factors come into play when considering the threats of today’s world coupled with the vulnerabilities of today’s technology.