Continuing from Part Two where we covered three of the four competencies within an organization and their procedures for audit readiness – Information Technology (IT) can turn out to be the most complex.
IT audit readiness may include, but is not limited to the following:
- Resource planning for the organization and readiness procedures
- IT General Controls
- IT Systems and application controls
IT resource planning for audit readiness
As discussed in part two of the audit readiness guide, one of the roles in the planning process is to help identify experienced team members who can contribute towards the IT department’s audit readiness, as they are the ones who have most likely undergone at least one or more IT audits. These individuals would be most familiar with the processes involved and would understand what the auditors would be requesting, the types of audits they would run, and the systems and applications involved.
Identifying IT internal systems and applications for audit readiness
Audit readiness activities for the IT environment require the identification and evaluation of in-scope systems within the organization. The organization should be tracking, recording and reporting on any activities taking place that involve the selected systems and/or applications involved in the audit readiness plan and within any department reliant on these the IT systems.
Activities may include:
- Documented system certification and accreditation packages
- Plans regarding system or application security controls
- Project plans and/or agreements on any application interfaces
- IT compliance procedures
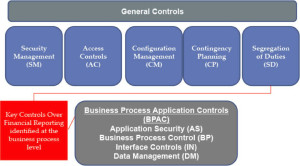
Once the appropriate systems and applications have been identified, the audit process should move onto assessing the following two groups of controls:
- IT general controls
- IT application controls
IT general controls and IT applications controls
The objective or intent of IT General Controls (ITGC) is to apply assurance over the system environment(s) of in-scope systems and/or applications. The ITGCs establish the integrity of:
- Processes and computer operations
- Data and data files
- Components and programs
ITGCs most commonly known are:
- Computer operations controls
- Data recover and backup controls
- Data center security controls
- Program management and program change management controls
- SDLC also known as system development lifecycle controls
- Access controls for data, applications and infrastructure
Furthermore, the objective or intent for IT application controls is to apply control(s) over an individual application or system, intending to support business processes.
Consideration and preparation are key to any audit assessment. Ensuring the organization’s environments, systems and applications are identified and assessed will improve the overall efficiency during any audit or assessment related activity.
Global Shield IS specializes in IT audit readiness procedures. We are a global audit and advisory services company ready to help you become audit ready. Contact us today for advice.
Please note: These guidelines from Global Shield IS, are for an organization’s general information purposes only. It is not intended to advise or give any legal or business analysis. Global Shield IS, rather offers the services to any business who have further questions related to their uncommon or unique circumstances, to contact the office for further council. We will then assign the most appropriate adviser to address each question specifically.